WA Leaders — Cyber Exposure Snapshot
What attackers already see when they drive past your business.
The drive-by view of WA Leaders
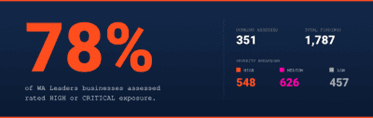
Cyber Node recently ran a Cyber Exposure Snapshot across 351 WA Leaders member and member-adjacent domains. Nobody was billed, nobody was asked, and nothing was touched — no credentials used, no internal systems accessed. We simply looked at what the public internet already says about each business, the same way an attacker does before any real intrusion.
We’re sharing the results because Australian SMBs are sitting on easily-fixed exposure that they almost certainly don’t know about — and the results are confronting.
What the drive-by sees
Six recurring themes account for the bulk of the 1,787 findings. None are exotic. All are fixable — usually by your existing IT provider, in days, once they know the issue exists.
| Exposure |
What it means in plain English | |
| 1 |
Email impersonation wide open |
Anyone can send email that looks like it came from your domain. Invoice fraud starts here. |
| 2 |
Staff credentials in breach corpora |
Corporate logins (and sometimes passwords) already searchable online. |
| 3 |
Login portals & admin panels exposed |
Often advertising the exact software version — a free roadmap for attackers. |
| 4 |
End-of-life software on the perimeter |
Known, published vulnerabilities sitting unpatched. |
| 5 |
Hosting & control panels reachable globally |
One compromise hands over website, email and DNS. |
| 6 | Forgotten subdomains & staging environments | The digital side gate nobody remembers installing. |
Why this isn’t your MSP’s job
Your IT provider keeps things working — uptime, backups, email flowing. Cyber Node looks at what could break the business, from the outside, the way an attacker does. Different trade, different mindset.
The Snapshot gives your MSP a prioritised, attacker’s-eye to-do list. It makes their job easier, not harder.
What it costs the business if ignored
• Invoice fraud & payment redirection — the #1 cyber loss for Australian SMBs
• Business email compromise via reused breached passwords
• Reputational damage from phishing sent under your domain
• Cyber insurance friction — insurers now check external posture before paying claims
Most fixes are configuration changes, not capital projects. The cost of acting is a fraction of the cost of not.
What to do this week
1. Run your own Snapshot at app.cybernode.au — 2 minutes, non-intrusive, free.
2. Hand the report to your IT provider as a shared to-do list.
3. Re-run quarterly — exposure isn’t static.

